GridinSoft Threat Intelligence
ML-BL switch teams.exe threat report
GridinSoft Anti-Malware detection
Detected by GridinSoft before you download
The current ThreatInfo record shows this exact file hash detected as Trojan.Heur!. Download GridinSoft Anti-Malware to scan the device, confirm whether this file is present, and remove the detected object if it is found.
- Detection name
- Trojan.Heur!
- Recommended action
- Scan and remove
- Last analysis
- 2026-04-16 23:00:36 (a month ago)
- File hash
- 7122f674dafc710c1eac0beb54530d57
Why it matters
Why GridinSoft flags this file
GridinSoft identifies the sample as Trojan.Heur!, part of the Trojan threat category.
Malware disguised as legitimate software or delivered through deceptive packaging. Related Trojan reports help compare this file with nearby detections, publishers, and hashes.
First seen 2026-04-16 23:00:36 (a month ago); latest analysis 2026-04-16 23:00:36 (a month ago).
Company metadata: GZ8 ML Switch. Product metadata: GZ8 ML Switch.
ThreatInfo has seen this file in user or system paths listed below. Unexpected locations increase the need for local verification.
Recommended action
What to do next
- Compare the MD5 above with the file found on the device.
- Check whether the file appears in the observed locations or under one of the alternate names.
- Run GridinSoft Anti-Malware to confirm the detection and remove the file if it is present. Review the Trojan category for related samples and common context.
File context
ML-BL switch teams.exe is a Windows file recorded in the ThreatInfo database. It is associated with GZ8 ML Switch. The reported company name is GZ8 ML Switch. The current detection status is Trojan.Heur!, based on the latest analysis from 2026-04-16 23:00:36 (a month ago). ThreatInfo groups this verdict with Trojan reports for broader family-level investigation.
If ML-BL switch teams.exe appears on your computer unexpectedly, treat it as suspicious. Check its location, digital signature, and recent system changes before allowing it to run. A full anti-malware scan is recommended when this file is detected as Trojan.Heur!.
File Details
| Product Name: | GZ8 ML Switch |
| Company Name: | GZ8 ML Switch |
| MD5: | 7122f674dafc710c1eac0beb54530d57 |
| Size: | 164 MB |
| First Published: | 2026-04-16 23:00:36 (a month ago) |
| Latest Published: | 2026-04-16 23:00:36 (a month ago) |
| Status: | Trojan.Heur! (on last analysis) | |
| Analysis Date: | 2026-04-16 23:00:36 (a month ago) |
Detection screenshot
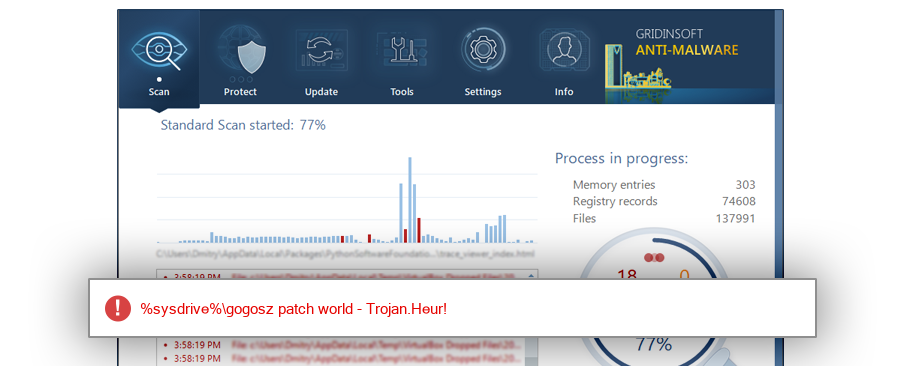
The screenshot is a visual record of a GridinSoft Anti-Malware detection for this sample. Use the hash and metadata above as the primary identifiers when comparing the file on your system.
Common Places:
| %sysdrive%\gogosz patch world |
ThreatInfo has observed ML-BL switch teams.exe in the locations listed above. Files found in temporary folders, user profile folders, startup locations, or unusual application directories should be reviewed more carefully than files installed under a known program directory.
Geographic signal
Observed country distribution
ThreatInfo has seen ML-BL switch teams.exe across 1 countries. Use this signal to compare local evidence with where the sample is most often reported.
The strongest geographic signal for this file is Brazil with 100.0% of observed hits. Geographic distribution can help identify targeted campaigns, regional software bundles, or where a file is most commonly reported.
OS Version:
The most common operating system signal for ML-BL switch teams.exe is Windows 10 with 100.0% of observed hits. If your system differs from the common profile, check whether the file was introduced by a specific installer, archive, or removable device.
Analysis
ML-BL switch teams.exe is identified as pe for 64-bit systems. The subsystem is Windows GUI. PE header values are useful for triage, especially when they do not match the expected publisher, product, or release timeline.
PE Sections:
Section layout highlights raw-size concentration, repeated names, packer markers, and hashes that can be compared across related samples.
3ed5512b293aa5ccb14a2730a5a29785
97f56458aeb5042fc110de6a7f14cf6a
1eec5f75ef41c94c714f5fe92c9dbe83
bdbd47f50acb588f18109210cc948292
37812f81534460a128d06d0d29b2cb00
5e719284ea9e10e425eb098bcb92041e
ffd9e639699de5fb134c50bd541ebbe9
c017b40200f8c9874f8b537e05c341f2
PE section names and hashes can reveal packing, injected resources, or unusual build artifacts. Sections with uncommon names, very large raw data, or hashes that differ from a trusted copy deserve additional review.
Report conclusion
GridinSoft detects this file as Trojan.Heur!
This report identifies ML-BL switch teams.exe by MD5 7122f674dafc710c1eac0beb54530d57. It is part of the Trojan report group. If the same file is present on your device, scan the system and remove the detected object after confirming the hash and location.