GridinSoft Threat Intelligence
f4057392.exe threat report
GridinSoft Anti-Malware detection
Detected by GridinSoft before you download
The current ThreatInfo record shows this exact file hash detected as Trojan.Generic. Download GridinSoft Anti-Malware to scan the device, confirm whether this file is present, and remove the detected object if it is found.
- Detection name
- Trojan.Generic
- Recommended action
- Scan and remove
- Last analysis
- 2023-04-01 23:09:50 (3 years ago)
- File hash
- 40872bbb9f0737cce4659361747de489
Why it matters
Why GridinSoft flags this file
GridinSoft identifies the sample as Trojan.Generic.
First seen 2023-04-01 23:06:57 (3 years ago); latest analysis 2023-04-01 23:09:50 (3 years ago).
Company metadata: Advanced Micro Devices, Inc.. Product metadata: ATI Radeon Family.
ThreatInfo has seen this file in user or system paths listed below. Unexpected locations increase the need for local verification.
Recommended action
What to do next
- Compare the MD5 above with the file found on the device.
- Check whether the file appears in the observed locations or under one of the alternate names.
- Run GridinSoft Anti-Malware to confirm the detection and remove the file if it is present.
File context
f4057392.exe is a Windows file recorded in the ThreatInfo database. It is associated with ATI Radeon Family. The reported company name is Advanced Micro Devices, Inc.. The current detection status is Trojan.Generic, based on the latest analysis from 2023-04-01 23:09:50 (3 years ago).
If f4057392.exe appears on your computer unexpectedly, treat it as suspicious. Check its location, digital signature, and recent system changes before allowing it to run. A full anti-malware scan is recommended when this file is detected as Trojan.Generic.
File Details
| Product Name: | ATI Radeon Family |
| Company Name: | Advanced Micro Devices, Inc. |
| MD5: | 40872bbb9f0737cce4659361747de489 |
| Size: | 20 MB |
| First Published: | 2023-04-01 23:06:57 (3 years ago) |
| Latest Published: | 2023-04-01 23:09:50 (3 years ago) |
| Status: | Trojan.Generic (on last analysis) | |
| Analysis Date: | 2023-04-01 23:09:50 (3 years ago) |
Detection screenshot
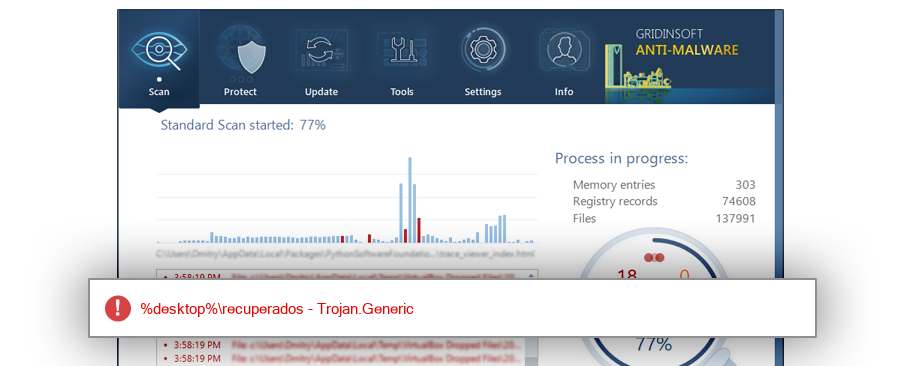
The screenshot is a visual record of a GridinSoft Anti-Malware detection for this sample. Use the hash and metadata above as the primary identifiers when comparing the file on your system.
Common Places:
| %desktop%\recuperados |
ThreatInfo has observed f4057392.exe in the locations listed above. Files found in temporary folders, user profile folders, startup locations, or unusual application directories should be reviewed more carefully than files installed under a known program directory.
Geographic signal
Observed country distribution
ThreatInfo has seen f4057392.exe across 1 countries. Use this signal to compare local evidence with where the sample is most often reported.
The strongest geographic signal for this file is Mexico with 100.0% of observed hits. Geographic distribution can help identify targeted campaigns, regional software bundles, or where a file is most commonly reported.
OS Version:
The most common operating system signal for f4057392.exe is Windows 10 with 100.0% of observed hits. If your system differs from the common profile, check whether the file was introduced by a specific installer, archive, or removable device.
Analysis
f4057392.exe is identified as pe for 64-bit systems. The subsystem is Native. PE header values are useful for triage, especially when they do not match the expected publisher, product, or release timeline.
PE Sections:
Section layout highlights raw-size concentration, repeated names, packer markers, and hashes that can be compared across related samples.
886c3cac2717d2e857491e444661860b
620ee03956631375045deda404c4b081
c8cd84a21bf99b3dee37529021980485
d8dc8d7f1bab58ea2b0c97a035eb55b1
f6e0cb012731a58ca43d7a1c57817a9d
b89a8a5a3e8a4ad00ad53a38628c9c51
39f42fa96c42b8b85849e62d36582d70
dee4c703308288cff06912f6087f2a35
82c2c8a9afb075feaa4970815fc8f0a1
d6c3ec52155f6ac583d28cc151655830
ef86c924672e107c23bbb966e6bec65f
7754bd4203c52e8681643b7667cd7fec
099b3030d6c11b6fc3716de5d56c473e
cf52814689be9f6db85ea803656fe714
b32da3862fde3a81e917673ff0442549
e1b37fb339123e8d9531bde54e083b11
cb9676488c7d0e02adee43e2fbf93055
09de8cdddd5c872865374c2fc10e2add
fcfd48b56b6c23df6ed66a53ce91950e
900f79484d43c36dac4692432b53afd4
19fd09ad01ad50c77b5f5b333a2b2633
a29fcb2a9230f5f7a29bbed3149e0e00
cf7e2fbac8a6b8fcf74fc0846f78e8b1
e08b4ed26c20b32c57090cbbe0c986f8
ec6484f7e946e488defec670f8f28add
40399c59e20db16c5e9a4bc7c07c8da1
aeab674afb6a83fd40df9fc5fea8a2e0
ec6bf45369ecbe371c567cb39b0a85e8
cc9c71489ff873be270f75b5d1ce2327
044b19790838b814b8ca292516ed004b
78f9fa9b43f3ab3ec832703bf012660c
f508ecb2481ad9ed7baf84b3b97c408d
6f6d509410d908d2f7f07b9748943e99
7106f475f23b5d47af6d936e75c6c178
d16e4514cf3b37f4ba0d2a19c885343a
53be74d7e649d7385b6e1f701680f613
56552307dff1972b09390cf572395b17
638854d0e75387141670347f1927de04
c1e150387b94f82e310cff5a1c36e937
43c9b3b673293c5fdae46373757da56c
db8ef16cda25bf53dc2c2006f74683b1
fa8fc4ff78def4ead19ccb22e38b3e4a
0876124b3748e14a6d49c025fd2d3e2c
ea94bea44beef3fabb54315acb684a83
6e05dd277d2db0612a8abd4bf1ac9d19
379d603b0dc083e659b3046715aa9076
de28da3c5a6a608ff08445b1d9c1c59a
19ec3e37642a06b5ad185c75c9799871
a7a68b96f38b6291d6d4395eb0bb20df
03022ce95ee691912573f0da72e639a5
d17336ee70cae7a5c96591e22289bac1
c99e897260240c3e3db2e08658567e27
0a63af97ab654b8fc45edfde4960b94a
1cdd3d21e59190652d8c231796209c98
8d2a69e8860436d8da3e74db45c5de04
PE section names and hashes can reveal packing, injected resources, or unusual build artifacts. Sections with uncommon names, very large raw data, or hashes that differ from a trusted copy deserve additional review.
Report conclusion
GridinSoft detects this file as Trojan.Generic
This report identifies f4057392.exe by MD5 40872bbb9f0737cce4659361747de489. If the same file is present on your device, scan the system and remove the detected object after confirming the hash and location.