GridinSoft Threat Intelligence
atikmdag.sys threat report
GridinSoft Anti-Malware detection
Detected by GridinSoft before you download
The current ThreatInfo record shows this exact file hash detected as Trojan.Generic. Download GridinSoft Anti-Malware to scan the device, confirm whether this file is present, and remove the detected object if it is found.
- Detection name
- Trojan.Generic
- Recommended action
- Scan and remove
- Last analysis
- 2024-11-14 23:00:55 (a year ago)
- File hash
- f701c5b11809d8930bfcda246023cafc
Why it matters
Why GridinSoft flags this file
GridinSoft identifies the sample as Trojan.Generic.
First seen 2024-09-16 23:07:24 (2 years ago); latest analysis 2024-11-14 23:00:55 (a year ago).
Company metadata: Advanced Micro Devices, Inc.. Product metadata: ATI Radeon Family.
ThreatInfo has seen this file in user or system paths listed below. Unexpected locations increase the need for local verification.
Recommended action
What to do next
- Compare the MD5 above with the file found on the device.
- Check whether the file appears in the observed locations or under one of the alternate names.
- Run GridinSoft Anti-Malware to confirm the detection and remove the file if it is present.
File context
atikmdag.sys is a Windows file recorded in the ThreatInfo database. It is associated with ATI Radeon Family. The reported company name is Advanced Micro Devices, Inc.. The current detection status is Trojan.Generic, based on the latest analysis from 2024-11-14 23:00:55 (a year ago).
If atikmdag.sys appears on your computer unexpectedly, treat it as suspicious. Check its location, digital signature, and recent system changes before allowing it to run. A full anti-malware scan is recommended when this file is detected as Trojan.Generic.
File Details
| Product Name: | ATI Radeon Family |
| Company Name: | Advanced Micro Devices, Inc. |
| MD5: | f701c5b11809d8930bfcda246023cafc |
| Size: | 25 MB |
| First Published: | 2024-09-16 23:07:24 (2 years ago) |
| Latest Published: | 2024-11-14 23:00:55 (a year ago) |
| Status: | Trojan.Generic (on last analysis) | |
| Analysis Date: | 2024-11-14 23:00:55 (a year ago) |
Detection screenshot
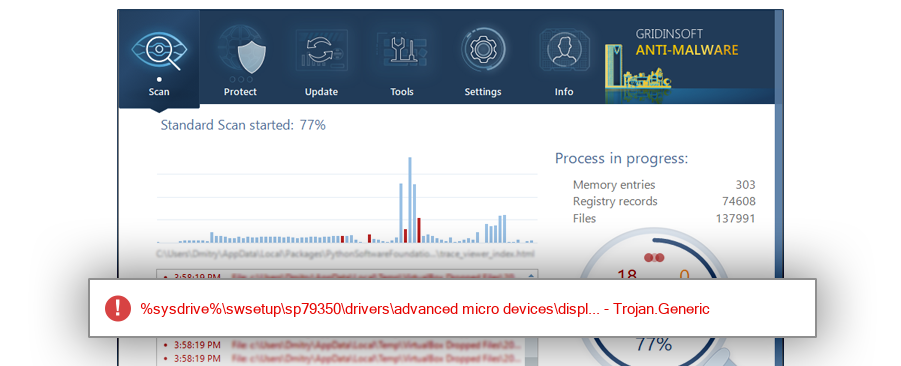
The screenshot is a visual record of a GridinSoft Anti-Malware detection for this sample. Use the hash and metadata above as the primary identifiers when comparing the file on your system.
Common Places:
| %sysdrive%\swsetup\sp79350\drivers\advanced micro devices\display\c7302645.inf_amd64_f6f8d780c3abe506 |
| %sysdrive%\swsetup\sp79350\drivers\advanced micro devices\display\c0302645.inf_amd64_7c75f5e09460e4d3 |
ThreatInfo has observed atikmdag.sys in the locations listed above. Files found in temporary folders, user profile folders, startup locations, or unusual application directories should be reviewed more carefully than files installed under a known program directory.
Geographic signal
Observed country distribution
ThreatInfo has seen atikmdag.sys across 2 countries. Use this signal to compare local evidence with where the sample is most often reported.
The strongest geographic signal for this file is Venezuela with 50.0% of observed hits. Geographic distribution can help identify targeted campaigns, regional software bundles, or where a file is most commonly reported.
OS Version:
The most common operating system signal for atikmdag.sys is Windows 10 with 100.0% of observed hits. If your system differs from the common profile, check whether the file was introduced by a specific installer, archive, or removable device.
Analysis
atikmdag.sys is identified as pe for 64-bit systems. The subsystem is Native. PE header values are useful for triage, especially when they do not match the expected publisher, product, or release timeline.
PE Sections:
Section layout highlights raw-size concentration, repeated names, packer markers, and hashes that can be compared across related samples.
ed0e85db8f4a31f97d4eaca23d6915d0
9fa1eb6fcb2f50db0348f8fbf88e8935
0fa4182a034fd437c326a34349739310
db694c70a0f7aaad384ec5a91cb55d16
b6873717c6f6feb8b1d6b0e64d7cc8ba
004a16016cde97d53cf863fe613eff93
d1b6248a0db239582006fd15c9f6fa6c
7037911d9aea54178ce6e23d741d15ff
b4ba8b8a79c162c0aecd54cfbb6d8cfb
f0ef208b1ec300e406211f40abbb5296
ed9ab23563efc16b86b4d91ff2cd6923
6ce224013698b4745f2ebb4b11280216
eff9f5dde95d4df3bc2410f0b85a2741
453d0cdfec5129a40b66e937b724c49f
0558140d53e482163a021da2335fe3f9
346a47eb033e42ac275230ebc01c3e54
6a09d2a0adad34f6c86081eff9e0cedf
1e912bbf6886a6beff89087f10ae48e8
997a543d8132d035ea3befe88c53b82e
fcfc4262587f3a280951a43a69d59a1a
a7cb2c6e50e50380e58b655988d60065
c3dadc0d6346251f2d8a323360c21d97
b82dccf716217780bcb87cda7681a7c8
51b17ce46db279a3c1fba9c31475c041
466380aa3ad6ee8a137f94f5fc7c72b6
74f1526dba69c7c4962ccc4e8b21699c
c1f6d593fe1e31b227e4c6144bb3cadb
06b89c4de713d95760584033099bc0dd
3f1cae4882e8376b7303b05b8670cd6c
b35cef1799098df733e21b7992396c4e
5bfa226648781be4edd5a812f3556f74
25d3cef81f30f79d7f64e9840e8a3b3d
62a8aeb8ec89f9fcd71f65b729d7a531
a1f6c16f980a2b68965ef10c5a8fef29
89db38238c6c75d89698387ddbcb3221
bd992eb38acd49b9ee3d3eff9734c5e2
a0b5a6493aabb02c3168e7e0a8dfccdb
d31b92c037f24edeb4e73651b79f1808
63795aa53701b15b361631ee2aac135d
73e8a1f95db973ba3155083c3a09d148
c4cb8fcf5950d495868fd0463ee6fdc3
2af5eb141af5c2b7013534959af7a241
23faba6c798f0e36b079d60ca3bac509
215bb1e25359041021e420bf71137d7a
20e2b259195127d715de724020f5a974
8a2b15060c0fcb5754362062adfcbeb3
f3719eae7f4145170787a75eb0e91872
4e70a42a048d01579daadde814fed4a2
7da716477c3ef67c56ef4319cf84bef7
b73a35125ac60d0b49c6d11dab48b3ae
618aa5d833d2ba9f13fdcccfee8c9dcb
09a03280ed698b2d943505ae060df3c5
d9b2739308eda672dd7d82f49452b9ec
da042f966e056debb50504d84cd2f729
38ec39c44cfa77cf5d7c2ddd72d2cbac
59bf2611b25e1960a42fd59dd1b04386
8e6c836ca0d20e391c15a5c74a9c50a8
a7ece5edad49ee42fd2311c8b8a73d04
b621ecd8397371448b39aa75005278a7
65380ffa4edce459c61d0d35b8222250
c1c467dedfa52a91c4dc393831efc3d7
e6ffed0f14fe7f1df5e48dcc734c1f61
da5ec897ec60c30cbd92339aa8a81e6f
PE section names and hashes can reveal packing, injected resources, or unusual build artifacts. Sections with uncommon names, very large raw data, or hashes that differ from a trusted copy deserve additional review.
Report conclusion
GridinSoft detects this file as Trojan.Generic
This report identifies atikmdag.sys by MD5 f701c5b11809d8930bfcda246023cafc. If the same file is present on your device, scan the system and remove the detected object after confirming the hash and location.