GridinSoft Threat Intelligence
atikmdag.sys threat report
GridinSoft Anti-Malware detection
Detected by GridinSoft before you download
The current ThreatInfo record shows this exact file hash detected as Trojan.Generic. Download GridinSoft Anti-Malware to scan the device, confirm whether this file is present, and remove the detected object if it is found.
- Detection name
- Trojan.Generic
- Recommended action
- Scan and remove
- Last analysis
- 2025-06-12 23:00:57 (11 months ago)
- File hash
- 048c310f865c762d76ce807f9d022cea
Why it matters
Why GridinSoft flags this file
GridinSoft identifies the sample as Trojan.Generic.
First seen 2025-06-12 23:00:57 (11 months ago); latest analysis 2025-06-12 23:00:57 (11 months ago).
Company metadata: Advanced Micro Devices, Inc.. Product metadata: ATI Radeon Family.
ThreatInfo has seen this file in user or system paths listed below. Unexpected locations increase the need for local verification.
Recommended action
What to do next
- Compare the MD5 above with the file found on the device.
- Check whether the file appears in the observed locations or under one of the alternate names.
- Run GridinSoft Anti-Malware to confirm the detection and remove the file if it is present.
File context
atikmdag.sys is a Windows file recorded in the ThreatInfo database. It is associated with ATI Radeon Family. The reported company name is Advanced Micro Devices, Inc.. The current detection status is Trojan.Generic, based on the latest analysis from 2025-06-12 23:00:57 (11 months ago).
If atikmdag.sys appears on your computer unexpectedly, treat it as suspicious. Check its location, digital signature, and recent system changes before allowing it to run. A full anti-malware scan is recommended when this file is detected as Trojan.Generic.
File Details
| Product Name: | ATI Radeon Family |
| Company Name: | Advanced Micro Devices, Inc. |
| MD5: | 048c310f865c762d76ce807f9d022cea |
| Size: | 20 MB |
| First Published: | 2025-06-12 23:00:57 (11 months ago) |
| Latest Published: | 2025-06-12 23:00:57 (11 months ago) |
| Status: | Trojan.Generic (on last analysis) | |
| Analysis Date: | 2025-06-12 23:00:57 (11 months ago) |
Detection screenshot
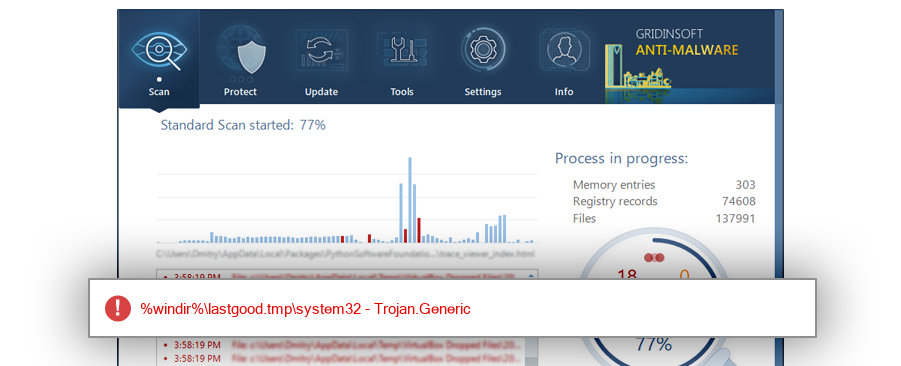
The screenshot is a visual record of a GridinSoft Anti-Malware detection for this sample. Use the hash and metadata above as the primary identifiers when comparing the file on your system.
Common Places:
| %system%\driverstore\filerepository\c0180730.inf_amd64_5f9cf4cab41b6065 |
| %sysdrive%\windows.old\windows\system32\driverstore\filerepository\c0180730.inf_amd64_5f9cf4cab41b6065 |
| %windir%\lastgood.tmp\system32 |
ThreatInfo has observed atikmdag.sys in the locations listed above. Files found in temporary folders, user profile folders, startup locations, or unusual application directories should be reviewed more carefully than files installed under a known program directory.
Geographic signal
Observed country distribution
ThreatInfo has seen atikmdag.sys across 1 countries. Use this signal to compare local evidence with where the sample is most often reported.
The strongest geographic signal for this file is Philippines with 100.0% of observed hits. Geographic distribution can help identify targeted campaigns, regional software bundles, or where a file is most commonly reported.
OS Version:
The most common operating system signal for atikmdag.sys is Windows 10 with 100.0% of observed hits. If your system differs from the common profile, check whether the file was introduced by a specific installer, archive, or removable device.
Analysis
atikmdag.sys is identified as pe for 64-bit systems. The subsystem is Native. PE header values are useful for triage, especially when they do not match the expected publisher, product, or release timeline.
PE Sections:
Section layout highlights raw-size concentration, repeated names, packer markers, and hashes that can be compared across related samples.
4c368fa8bc8e30e19d2d229b1cb6fc93
f01283c6d3c08fa7afb01c4f511a4b0e
31edffbc25a5c742b512753d2525213e
f0810f0e8940bfc9c4435468cc3c5d8d
c4dfef5192e991c259dad297197b15e5
b8f05a0df5ed2474ce52e7452dae18ac
e7862d4b8a86938f6a012a7a1dcc5815
21d278c8fb4e9541a8dcf090166803af
b23345a8e14114f98ab52f6d2d1f049f
04231a04905cfc17bcfe60db1fa8d5d0
8863b5a69101b2a50eb77707e87ffc22
b72e046afdf5a09a960f50d5d46b59cb
ffb9ceee744da6d057e7f7a28cbb63de
c04e4835e58eac7631c1e4f944e79a73
6fca05508bdd193f94fd89c7328eeb64
fb7051c673615891439884878e22fc45
410982c7f577d0c7461ed4aec6e13c7a
a19d3bba988a5db77f85af4f70f68315
a7232f4a37f90d297b75f462cb0be08f
3064d3869776eb4afb0de8f7ef10a026
26204f312e61c1c291e6c163266ca852
268dbe2e5a7794402fbf09170d2a2955
04775439ed76c516f0cb281556ee134e
7b63af9b370bf4f2d23946c180eab608
a91f5e090897d8698d240a933facef0e
b43f7faa16603efaeec43f0505c1710f
771b3619a1c78ef87083ac032aad6e9a
845c3df230e5bb4c63a5641f03afdf89
d3aa44fea7736cf2aac0495ba7130a01
97e65da146783c15b534e8c4e7cf544c
12ce854d24582b22ae312aa5fb23a3ea
53fe6d6ac68f298427e18eb567e209a3
dadb69e3c483a2534fd4228e472bad0c
0495756012e7a47f780afeaea9f59e86
a4d05358fbea15c755f7e1dfb1b0dce0
ec2eaf71c6a2bbf45aaea32fa229b514
86e98f0e9d8be82ea83a262ec61ba3c7
e28171dde7eb088a3cbaa7176440ba06
c25d4b311ffa2211d638bacb212536af
992b53d4475b32ef2a5d671e5d78ec90
06553f7d198910f1a909bd9cf27459a9
aad86e6efa274707c62f87284c117a27
cb02b23e56eab75c1d090fc0d8827550
ac95ac403319b0d10ad6f5d4a0fc79a8
3c3db67534c46e451f4c9091540c6b25
36f07b19dc2f0163d0f08ce5d96c4b70
463d19e602c27e882e1dd2469c1329d7
cc0ced05fced2be3cd4457644970efd6
6c57c35bb7cbe8bee6adc45fef9173cf
191ab590bc07d9cef9dcfab2d72e92e3
e09cbfb14acb2a1186de027335bda301
c865e712ba39ebc795f5d7b7cad0bb16
33a6c80a7a93f5deaa294fed3e638a21
d074a3183ffec81a93a9f98bb83bd7de
PE section names and hashes can reveal packing, injected resources, or unusual build artifacts. Sections with uncommon names, very large raw data, or hashes that differ from a trusted copy deserve additional review.
Report conclusion
GridinSoft detects this file as Trojan.Generic
This report identifies atikmdag.sys by MD5 048c310f865c762d76ce807f9d022cea. If the same file is present on your device, scan the system and remove the detected object after confirming the hash and location.