GridinSoft Threat Intelligence
amdkmdag.sys threat report
GridinSoft Anti-Malware detection
Detected by GridinSoft before you download
The current ThreatInfo record shows this exact file hash detected as Trojan.Generic. Download GridinSoft Anti-Malware to scan the device, confirm whether this file is present, and remove the detected object if it is found.
- Detection name
- Trojan.Generic
- Recommended action
- Scan and remove
- Last analysis
- 2025-10-15 23:00:46 (7 months ago)
- File hash
- 4b7b9b7df5ce72f7725f38d82880062d
Why it matters
Why GridinSoft flags this file
GridinSoft identifies the sample as Trojan.Generic.
First seen 2025-10-15 23:00:46 (7 months ago); latest analysis 2025-10-15 23:00:46 (7 months ago).
Company metadata: Advanced Micro Devices, Inc. Product metadata: ATI Radeon Famil.
ThreatInfo has seen this file in user or system paths listed below. Unexpected locations increase the need for local verification.
Recommended action
What to do next
- Compare the MD5 above with the file found on the device.
- Check whether the file appears in the observed locations or under one of the alternate names.
- Run GridinSoft Anti-Malware to confirm the detection and remove the file if it is present.
File context
amdkmdag.sys is a Windows file recorded in the ThreatInfo database. It is associated with ATI Radeon Famil. The reported company name is Advanced Micro Devices, Inc. The current detection status is Trojan.Generic, based on the latest analysis from 2025-10-15 23:00:46 (7 months ago).
If amdkmdag.sys appears on your computer unexpectedly, treat it as suspicious. Check its location, digital signature, and recent system changes before allowing it to run. A full anti-malware scan is recommended when this file is detected as Trojan.Generic.
File Details
| Product Name: | ATI Radeon Famil |
| Company Name: | Advanced Micro Devices, Inc |
| MD5: | 4b7b9b7df5ce72f7725f38d82880062d |
| Size: | 79 MB |
| First Published: | 2025-10-15 23:00:46 (7 months ago) |
| Latest Published: | 2025-10-15 23:00:46 (7 months ago) |
| Status: | Trojan.Generic (on last analysis) | |
| Analysis Date: | 2025-10-15 23:00:46 (7 months ago) |
Detection screenshot
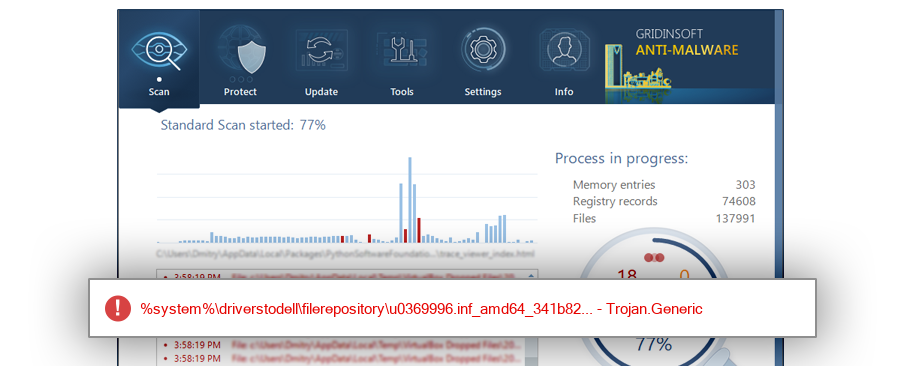
The screenshot is a visual record of a GridinSoft Anti-Malware detection for this sample. Use the hash and metadata above as the primary identifiers when comparing the file on your system.
Common Places:
| %system%\driverstodell\filerepository\u0369996.inf_amd64_341b825757693c75 |
ThreatInfo has observed amdkmdag.sys in the locations listed above. Files found in temporary folders, user profile folders, startup locations, or unusual application directories should be reviewed more carefully than files installed under a known program directory.
Geographic signal
Observed country distribution
ThreatInfo has seen amdkmdag.sys across 1 countries. Use this signal to compare local evidence with where the sample is most often reported.
The strongest geographic signal for this file is Canada with 100.0% of observed hits. Geographic distribution can help identify targeted campaigns, regional software bundles, or where a file is most commonly reported.
OS Version:
The most common operating system signal for amdkmdag.sys is Windows 10 with 100.0% of observed hits. If your system differs from the common profile, check whether the file was introduced by a specific installer, archive, or removable device.
Analysis
amdkmdag.sys is identified as pe for 64-bit systems. The subsystem is Native. PE header values are useful for triage, especially when they do not match the expected publisher, product, or release timeline.
PE Sections:
Section layout highlights raw-size concentration, repeated names, packer markers, and hashes that can be compared across related samples.
8ed80e0f69665d481067caf04225b595
902e61982b8b3184c186cbd3d967d7be
81e436e2d26d6c4b733a876aed139603
ff7a83680f63195c1a7bb541fe161dfc
4c023024ceb6894dad44f1ad65b3b6ba
57bdb0e1674a8801487a41c3b75d796c
c9fa8f065f319d71f476d53283a50a4c
a0526a925380f78f49460d42fc5d3c13
113ff5f3c62fb90730bc239c8b471810
f6bfdaa7e60260837e29673285766108
2130e88a8dbb28756862ca736f303c09
63e76748fff5ae03662c0c1134b8ffb2
9473845499f2dcf16746f32d667a4d5f
2674cdd2632528aab30117a934ea1b8b
c4d2d0e8e5ec194c423c1e9bc1d4b573
308c2e689e5f9fd61513cdba1d31dfe8
814aa7609ac54967afb3c9c0425e6ea0
833495571285a1827fc96248c493a095
2d33f5e6b4a9b6faf862b17ba66ccae5
32f28db4f975c1ede5d49bc404b76c5a
89531721b244a717456832a64806cd93
7aeff974acb2a5af0faf8b75df7b46fa
17bce3dd519fc394301c59cfd42615e6
225dd7a01d60e13472eed90d27063c64
b1ddbfc3637e43e35622636096909a3a
c8df284520f95e2289a55952c06cee7a
e6d1e0c84c71b644e51d52766cb57a4f
e5562ae7b29416425957f63b7f3d5ba9
b94007b6988557708bc35d10bd7a7a3f
7048a2df0f48e146181e3dad1ab6c337
e77591eefc881de88ca3d9af93e6d034
6f28db7815664c3323b28ee36a4ae9a7
4777efcdd5d1b29652a38dbcab8a7e05
7825344400ac7a70195f39f2bf194341
1f6747babbc3a84db243fe18cfdea9ae
24d3a652fa326dfa2c396b73f69a94d5
14f15f17b5762ca1633216fdcb14a41d
f0ed1398c16387f75b5270c86fc4b1d1
c5b4271026278a6bd4af44b183b0cd28
4f7346d8d502ec5d5232cc7eff9f2e35
bce87ef823d81edb938f307b79a2a233
d55a48fdf4213b4d1c995d7872090f5f
5d327fa2cdd371e2556d829309ff77de
23d0b27498292adc933284c39518cc86
a2c82f844bec4abc68531fbb41071d08
f0a9c2e6d8cb297f2fe411fb5b4640c4
ae64aed642e9619c4a6c4e5dc95605d9
a99b2610ae97987e784636f01691131a
a1130d31580563f23137c8ec062ef4aa
e1ce7f438f895169444bf3029742c1b7
ca01e015f8e4569ddef0eccc257540bb
c5957fa82236e32a956df8ebaf2b550c
3e8a3a1e5f57720965b49d631e331e13
e2a749e6936d6e8d5a9ebd646d75d533
dcbef2b96ddd4a971e790bc721b00749
7a16e51c18c94c387b4035b857c2e7bf
cb27d82020af6cf28df2f978cecde771
95e13575689ab1a43e0dcf79cfd3bbd6
PE section names and hashes can reveal packing, injected resources, or unusual build artifacts. Sections with uncommon names, very large raw data, or hashes that differ from a trusted copy deserve additional review.
Report conclusion
GridinSoft detects this file as Trojan.Generic
This report identifies amdkmdag.sys by MD5 4b7b9b7df5ce72f7725f38d82880062d. If the same file is present on your device, scan the system and remove the detected object after confirming the hash and location.