GridinSoft Threat Intelligence
$RAOPYQT.exe threat report
GridinSoft Anti-Malware detection
Detected by GridinSoft before you download
The current ThreatInfo record shows this exact file hash detected as Hack.KMS. Download GridinSoft Anti-Malware to scan the device, confirm whether this file is present, and remove the detected object if it is found.
- Detection name
- Hack.KMS
- Recommended action
- Scan and remove
- Last analysis
- 2025-03-16 23:01:11 (a year ago)
- File hash
- 8c69830a50fb85d8a794fa46643493b2
Why it matters
Why GridinSoft flags this file
GridinSoft identifies the sample as Hack.KMS, part of the Hack threat category.
Tools used to bypass protections, alter software behavior, or enable unauthorized access. Related Hack reports help compare this file with nearby detections, publishers, and hashes.
First seen 2017-08-04 20:04:33 (8 years ago); latest analysis 2025-03-16 23:01:11 (a year ago).
Signed by WZTeam. The signature is reported as valid, but signed files can still be bundled or abused.
This hash has appeared under multiple file names, which can happen with repackaging, bundling, or deliberate renaming.
ThreatInfo has seen this file in user or system paths listed below. Unexpected locations increase the need for local verification.
Recommended action
What to do next
- Compare the MD5 above with the file found on the device.
- Check whether the file appears in the observed locations or under one of the alternate names.
- Run GridinSoft Anti-Malware to confirm the detection and remove the file if it is present. Review the Hack category for related samples and common context.
File context
$RAOPYQT.exe is a Windows file recorded in the ThreatInfo database. The current detection status is Hack.KMS, based on the latest analysis from 2025-03-16 23:01:11 (a year ago). ThreatInfo groups this verdict with Hack reports for broader family-level investigation.
If $RAOPYQT.exe appears on your computer unexpectedly, treat it as suspicious. Check its location, digital signature, and recent system changes before allowing it to run. A full anti-malware scan is recommended when this file is detected as Hack.KMS.
File Details
| MD5: | 8c69830a50fb85d8a794fa46643493b2 |
| Size: | 935 KB |
| First Published: | 2017-08-04 20:04:33 (8 years ago) |
| Latest Published: | 2025-03-16 23:01:11 (a year ago) |
| Status: | Hack.KMS (on last analysis) | |
| Analysis Date: | 2025-03-16 23:01:11 (a year ago) |
Detection screenshot
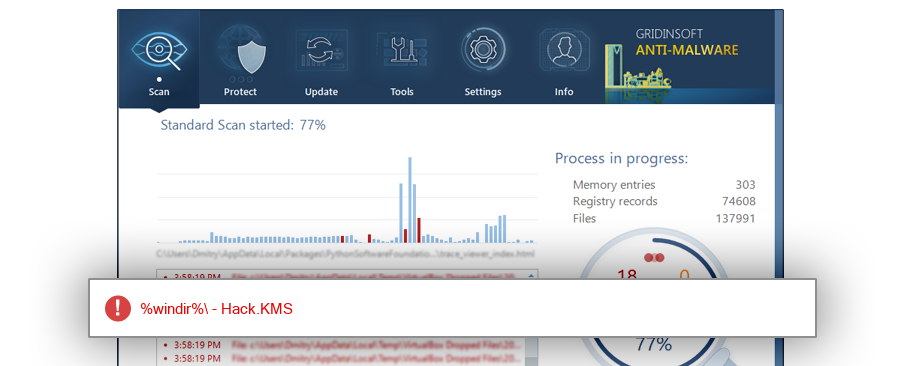
The screenshot is a visual record of a GridinSoft Anti-Malware detection for this sample. Use the hash and metadata above as the primary identifiers when comparing the file on your system.
Overview
| Signed By: | WZTeam |
| Status: | Valid |
The signature on $RAOPYQT.exe is reported as valid. A valid signature helps confirm publisher identity, but it does not automatically make the file safe if the installer was bundled, abused, or downloaded from an untrusted source.
Common Places:
| %sysdrive%\windows |
| %windir% |
| %temp% |
| %profile%\onedrive\桌面\office win啟動_activators\aact 3.3 portable |
| %profile%\downloads\activators |
| %sysdrive%\копия флешки 2018 февраль\новый софт 02.08.2016\активаторы |
| %sysdrive%\aktywator\aact 3.3 portable |
| %sysdrive%\программы\белов\beloff_2017.8\apps\!microsoft\kms |
| %desktop%\office win啟動_activators\aact 3.3 portable |
| %sysdrive%\microsoft\aact_v3.3_portable.zip |
ThreatInfo has observed $RAOPYQT.exe in the locations listed above. Files found in temporary folders, user profile folders, startup locations, or unusual application directories should be reviewed more carefully than files installed under a known program directory.
File Names:
4 observed namesThis hash has been seen with multiple file names. Alternate names can appear when software is updated, copied between folders, packed by an installer, or deliberately renamed to avoid recognition. Compare the exact MD5 above before assuming two names refer to the same file.
Geographic signal
Observed country distribution
ThreatInfo has seen $RAOPYQT.exe across 30 countries. Use this signal to compare local evidence with where the sample is most often reported.
The strongest geographic signal for this file is Russian Federation with 54.0% of observed hits. Geographic distribution can help identify targeted campaigns, regional software bundles, or where a file is most commonly reported.
OS Version:
The most common operating system signal for $RAOPYQT.exe is Windows 10 with 64.5% of observed hits. If your system differs from the common profile, check whether the file was introduced by a specific installer, archive, or removable device.
Analysis
$RAOPYQT.exe is identified as pe for 32-bit systems. The subsystem is Windows GUI. PE header values are useful for triage, especially when they do not match the expected publisher, product, or release timeline.
PE Sections:
Section layout highlights raw-size concentration, repeated names, packer markers, and hashes that can be compared across related samples.
fea284e6f5996bdc6e131c3453532759
897c57158e4aaaf015769d2723ea36cb
9b765409b44441dda4d87be207a6fe49
2c657ac5bb4ae4650b5d7049edcbce85
56f3d42cdc369a72a73d0175ed75f808
PE section names and hashes can reveal packing, injected resources, or unusual build artifacts. Sections with uncommon names, very large raw data, or hashes that differ from a trusted copy deserve additional review.
Report conclusion
GridinSoft detects this file as Hack.KMS
This report identifies $RAOPYQT.exe by MD5 8c69830a50fb85d8a794fa46643493b2. It is part of the Hack report group. If the same file is present on your device, scan the system and remove the detected object after confirming the hash and location.