GridinSoft Threat Intelligence
OCT3 Part 2.exe threat report
GridinSoft Anti-Malware detection
Detected by GridinSoft before you download
The current ThreatInfo record shows this exact file hash detected as Trojan.Heur!. Download GridinSoft Anti-Malware to scan the device, confirm whether this file is present, and remove the detected object if it is found.
- Detection name
- Trojan.Heur!
- Recommended action
- Scan and remove
- Last analysis
- 2024-08-16 23:12:04 (2 years ago)
- File hash
- a57c6e1e7473330c1d62399eaad81e53
Why it matters
Why GridinSoft flags this file
GridinSoft identifies the sample as Trojan.Heur!, part of the Trojan threat category.
Malware disguised as legitimate software or delivered through deceptive packaging. Related Trojan reports help compare this file with nearby detections, publishers, and hashes.
First seen 2024-08-16 23:12:00 (2 years ago); latest analysis 2024-08-16 23:12:04 (2 years ago).
Company metadata: Pacific Gold Coast Corp.. Product metadata: TurboSfx Application.
ThreatInfo has seen this file in user or system paths listed below. Unexpected locations increase the need for local verification.
Recommended action
What to do next
- Compare the MD5 above with the file found on the device.
- Check whether the file appears in the observed locations or under one of the alternate names.
- Run GridinSoft Anti-Malware to confirm the detection and remove the file if it is present. Review the Trojan category for related samples and common context.
File context
OCT3 Part 2.exe is a Windows file recorded in the ThreatInfo database. It is associated with TurboSfx Application. The reported company name is Pacific Gold Coast Corp.. The current detection status is Trojan.Heur!, based on the latest analysis from 2024-08-16 23:12:04 (2 years ago). ThreatInfo groups this verdict with Trojan reports for broader family-level investigation.
If OCT3 Part 2.exe appears on your computer unexpectedly, treat it as suspicious. Check its location, digital signature, and recent system changes before allowing it to run. A full anti-malware scan is recommended when this file is detected as Trojan.Heur!.
File Details
| Product Name: | TurboSfx Application |
| Company Name: | Pacific Gold Coast Corp. |
| MD5: | a57c6e1e7473330c1d62399eaad81e53 |
| Size: | 2 MB |
| First Published: | 2024-08-16 23:12:00 (2 years ago) |
| Latest Published: | 2024-08-16 23:12:04 (2 years ago) |
| Status: | Trojan.Heur! (on last analysis) | |
| Analysis Date: | 2024-08-16 23:12:04 (2 years ago) |
Detection screenshot
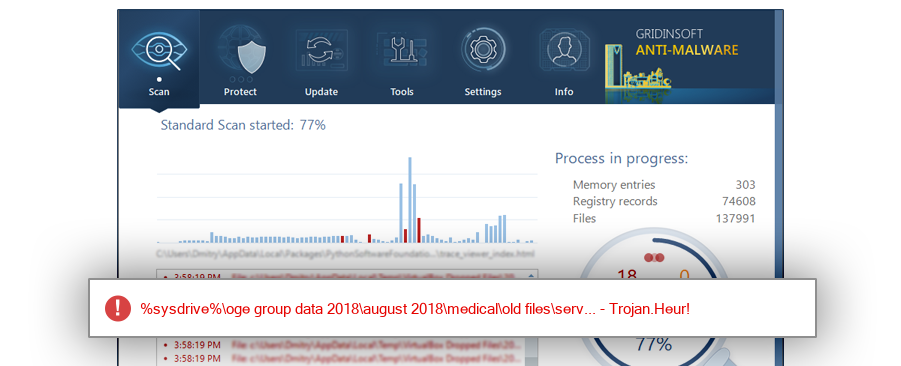
The screenshot is a visual record of a GridinSoft Anti-Malware detection for this sample. Use the hash and metadata above as the primary identifiers when comparing the file on your system.
Common Places:
| %sysdrive%\oge group data 2018\august 2018\medical\old files\service\misc data\asif backup\service\service manuals\zeiss\stratus oct3 |
| %sysdrive%\oge group data 2018\august 2018\medical\aoge medical\service\misc data\asif backup\service\service manuals\zeiss\stratus oct3 |
| %sysdrive%\oge group data 2018\august 2018\medical\aoge medical\service\service manuals\zeiss\stratus oct3 |
| %sysdrive%\oge group data 2018\august 2018\medical\old files\service\service manuals\zeiss\stratus oct3 |
ThreatInfo has observed OCT3 Part 2.exe in the locations listed above. Files found in temporary folders, user profile folders, startup locations, or unusual application directories should be reviewed more carefully than files installed under a known program directory.
Geographic signal
Observed country distribution
ThreatInfo has seen OCT3 Part 2.exe across 1 countries. Use this signal to compare local evidence with where the sample is most often reported.
The strongest geographic signal for this file is Egypt with 100.0% of observed hits. Geographic distribution can help identify targeted campaigns, regional software bundles, or where a file is most commonly reported.
OS Version:
The most common operating system signal for OCT3 Part 2.exe is Windows 10 with 100.0% of observed hits. If your system differs from the common profile, check whether the file was introduced by a specific installer, archive, or removable device.
Analysis
OCT3 Part 2.exe is identified as pe for 32-bit systems. The subsystem is Windows GUI. PE header values are useful for triage, especially when they do not match the expected publisher, product, or release timeline.
PE Sections:
Section layout highlights raw-size concentration, repeated names, packer markers, and hashes that can be compared across related samples.
aa5a7c3eea15854ace31ca2c1bd3c2de
d41d8cd98f00b204e9800998ecf8427e
de91e2e6062c02fc17345b336efa82d9
efe51d86bcbef3bfbcc0b0abcd85ec93
300e76d3b5976c4273383af35323202b
fa55ab578bdb4c4994fc13feda68d272
d6e8bf127a2df053ce71da96a444b33a
67aaf51bf95971033f5bb957d7304b28
e95dccbb452f7043c31bf98e6acb5d95
PE section names and hashes can reveal packing, injected resources, or unusual build artifacts. Sections with uncommon names, very large raw data, or hashes that differ from a trusted copy deserve additional review.
Report conclusion
GridinSoft detects this file as Trojan.Heur!
This report identifies OCT3 Part 2.exe by MD5 a57c6e1e7473330c1d62399eaad81e53. It is part of the Trojan report group. If the same file is present on your device, scan the system and remove the detected object after confirming the hash and location.