How to remove 26596 (2017_08_10 13_53_02 UTC).dll
- File Details
- Overview
- Analysis
26596 (2017_08_10 13_53_02 UTC).dll
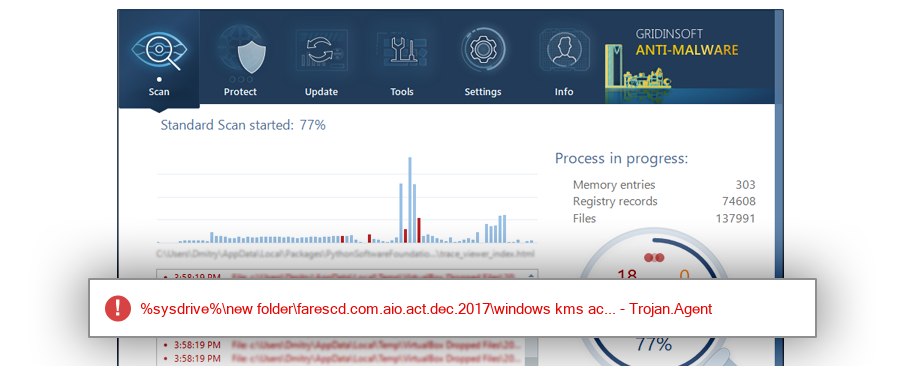
The module 26596 (2017_08_10 13_53_02 UTC).dll has been detected as Trojan.Agent
File Details
| MD5: |
0700c4ade6c694ae57f3364e31447b90 |
| Size: |
12 KB |
| First Published: |
2017-05-21 03:01:57 (7 years ago) |
| Latest Published: |
2024-05-24 23:01:38 (4 months ago) |
| Status: |
Trojan.Agent (on last analysis) |
|
| Analysis Date: |
2024-05-24 23:01:38 (4 months ago) |
| %windir%\system32 |
| %desktop%\kms啟動\32-bit |
| %profile%\downloads\compressed\dll_act\kms_vl_act.rar\kms_vl_act\32-bit |
| %temp%\rar$exa0.542\windows kms activator v3.1\kms_files\32-bit |
| %temp%\rar$exa0.540\windows kms activator v3.1\kms_files\32-bit |
| %windir%\setup\scripts\win32 |
| %desktop%\activate tool\win32 |
| %profile%\downloads\documents\kms_vl_all_6.6.1\kms_vl_all_6.6.1\32-bit |
| %profile%\dropbox\programlar\kms vl all 6.6.1.rar\kms vl all 6.6.1\32-bit |
| %profile%\dropbox\programlar\kms vl all 6.6.1\32-bit |
| SppExtComObjHook.dll |
| 26596 (2017_08_10 13_53_02 UTC).dll |
| sppextcomobjhook.dll |
| $RQGLFR3.dll |
| $R7QGVKY.dll |
| SPPEXTCOMOBJHOOK.DLL |
|
17.4% |
|
|
10.9% |
|
|
5.7% |
|
|
5.2% |
|
|
3.5% |
|
|
3.1% |
|
|
2.6% |
|
|
2.6% |
|
|
2.6% |
|
|
2.5% |
|
|
2.5% |
|
|
2.5% |
|
|
2.5% |
|
|
2.2% |
|
|
1.9% |
|
|
1.8% |
|
|
1.8% |
|
|
1.6% |
|
|
1.6% |
|
|
1.5% |
|
|
1.4% |
|
|
1.3% |
|
|
1.2% |
|
|
1.2% |
|
|
1.1% |
|
|
1.0% |
|
|
0.9% |
|
|
0.9% |
|
|
0.7% |
|
|
0.7% |
|
|
0.7% |
|
|
0.6% |
|
|
0.6% |
|
|
0.5% |
|
|
0.5% |
|
|
0.5% |
|
|
0.5% |
|
|
0.5% |
|
|
0.4% |
|
|
0.4% |
|
|
0.3% |
|
|
0.3% |
|
|
0.3% |
|
|
0.3% |
|
|
0.3% |
|
|
0.3% |
|
|
0.3% |
|
|
0.3% |
|
|
0.3% |
|
|
0.2% |
|
|
0.2% |
|
|
0.2% |
|
|
0.2% |
|
|
0.2% |
|
|
0.2% |
|
|
0.2% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
| Windows 10 |
74.0% |
|
| Windows 7 |
19.6% |
|
| Windows 8.1 |
5.0% |
|
| Windows Server 2012 R2 |
0.5% |
|
| Windows Embedded 8.1 |
0.3% |
|
| Windows Server 2008 R2 |
0.2% |
|
| Windows XP |
0.1% |
|
| Windows 8 |
0.1% |
|
| Windows Server 2016 |
0.1% |
|
Analysis
| Subsystem: |
Windows GUI |
| PE Type: |
pe |
| OS Bitness: |
32 |
| Image Base: |
0x10000000 |
| Entry Address: |
0x00002572 |
| Name |
Size of data |
MD5 |
| .text |
6144 |
61c42c5c0762691911dba3c2c96e61da |
| .rdata |
3584 |
33f50bb616a3f9bb756e563afbcbcbaf |
| .data |
1024 |
8f045343a3fd7b1e013c40d10d4e5d4c |
| .reloc |
512 |
2ce87c789e3f66de19957fd2706c138d |