How to remove kryptex4.exe
- File Details
- Overview
- Analysis
kryptex4.exe
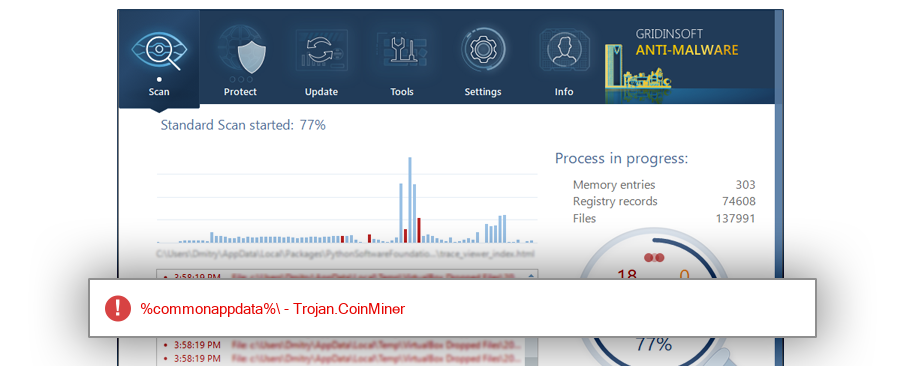
The module kryptex4.exe has been detected as Trojan.CoinMiner
File Details
| MD5: |
e685219f5704bd854d5ed6668b0e9146 |
| Size: |
2 MB |
| First Published: |
2017-05-21 13:07:51 (6 years ago) |
| Latest Published: |
2020-12-25 13:10:01 (3 years ago) |
| Status: |
Trojan.CoinMiner (on last analysis) |
|
| Analysis Date: |
2020-12-25 13:10:01 (3 years ago) |
| %windir%\fonts |
| %appdata%\kryptex\kryptex4 |
| %windir%\dell |
| %windir%\winsxslog |
| %windir%\winsxslog.rar\winsxslog |
| %windir%\tasks |
| %sysdrive%\windows |
| %sysdrive%\system volume information\systemrestore\frstaging\users\adnin1\appdata\roaming\kryptex\kryptex4 |
| %appdata%\claymore cryptonote cpu miner v3.5 beta - pool |
| %temp%\3537.tmp.zip\claymore cryptonote cpu miner v3.5 beta - pool |
| LMS.exe |
| kryptex4.exe |
| Update64.exe |
| SystemIISSec.exe |
| svchost.exe |
| NsCpuCNMiner64.exe |
| csrss.exe |
| NsCpuCNMiner.exe |
| acnom.exe |
| csrs.exe |
| conhosts.exe |
| wup.exe |
| csrss[1].exe |
| winlogon.exe |
| csrss.exe.quarantined |
| WUDFHost.exe |
| $RT05L8H.exe |
| qc64.exe |
| $RW6BHD2.exe |
| CMiner.exe |
| svc.exe |
| see64.exe |
| WUDFHost.exe.q_Quarantine_CB39827_q |
| HostManager.exe |
| smss.exe |
| serviceHost.exe |
| WindowsLocal.exe |
| $RG1VXTS.exe |
| srvan64.exe |
| mdx.exe |
| n11.exe |
| n113.exe |
| A0060589.exe |
| A0040401.exe |
| A0040381.exe |
| A0060509.exe |
| CPU_64.exe |
| SystemF0D7.exe |
| taskhost_32.exe |
| ccexplorer.exe |
| php5.exe |
| cpu.exe |
| EDMiner.exe |
| Csrsz.exe |
| System32.exe |
| Update_Windows.exe |
| qc64.exe.quarantined |
| winRARI.exe |
| RuntimeBroker.exe |
| update.exe |
| System64.exe |
| msqservice.exe |
| NSCPUCNMINER64.EXE |
| taskmgr.exe |
| msdc.exe |
| Fiddlere.exe |
| java.exe |
| Minings.exe |
| 64.exe |
| aspnet_state.exe |
| conhoste.exe |
| dether.exe |
| sys64.exe |
| msminer67.exe |
| cpu_64.exe |
|
19.2% |
|
|
11.4% |
|
|
10.2% |
|
|
9.7% |
|
|
8.0% |
|
|
7.2% |
|
|
5.9% |
|
|
3.0% |
|
|
2.7% |
|
|
2.3% |
|
|
2.0% |
|
|
1.4% |
|
|
1.0% |
|
|
1.0% |
|
|
1.0% |
|
|
0.8% |
|
|
0.7% |
|
|
0.7% |
|
|
0.7% |
|
|
0.7% |
|
|
0.7% |
|
|
0.5% |
|
|
0.5% |
|
|
0.5% |
|
|
0.4% |
|
|
0.4% |
|
|
0.4% |
|
|
0.4% |
|
|
0.4% |
|
|
0.4% |
|
|
0.4% |
|
|
0.4% |
|
|
0.3% |
|
|
0.3% |
|
|
0.3% |
|
|
0.3% |
|
|
0.3% |
|
|
0.3% |
|
|
0.3% |
|
|
0.3% |
|
|
0.3% |
|
|
0.3% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
|
0.1% |
|
| Windows 7 |
45.4% |
|
| Windows 10 |
22.3% |
|
| Windows Server 2008 R2 |
8.9% |
|
| Windows 8.1 |
7.9% |
|
| Windows XP |
4.4% |
|
| Windows Server 2012 |
4.2% |
|
| Windows Server 2012 R2 |
3.0% |
|
| Windows 8 |
1.4% |
|
| Windows Web Server 2008 R2 |
1.4% |
|
| Windows Server 2016 |
0.8% |
|
| Windows Server 2003 |
0.1% |
|
| Windows Embedded Standard |
0.1% |
|
| Windows Vista |
0.1% |
|
Analysis
| Subsystem: |
Windows CUI |
| PE Type: |
pe |
| OS Bitness: |
64 |
| Image Base: |
0x0000000140000000 |
| Entry Address: |
0x00595705 |
| Name |
Size of data |
MD5 |
| .text |
0 |
00000000000000000000000000000000 |
| .rdata |
0 |
00000000000000000000000000000000 |
| .data |
0 |
00000000000000000000000000000000 |
| .pdata |
0 |
00000000000000000000000000000000 |
| .tls |
512 |
bf619eac0cdf3f68d496ea9344137e8b |
| .vmp0 |
0 |
00000000000000000000000000000000 |
| .vmp1 |
2591744 |
1bf9de41767e43e1fa3870fb4481d4ea |
| .reloc |
512 |
b3c6b197b479fbffcb3085c61ff88ca4 |
| .rsrc |
1024 |
c4dca5f4fff0de08fa2dc903604ca303 |